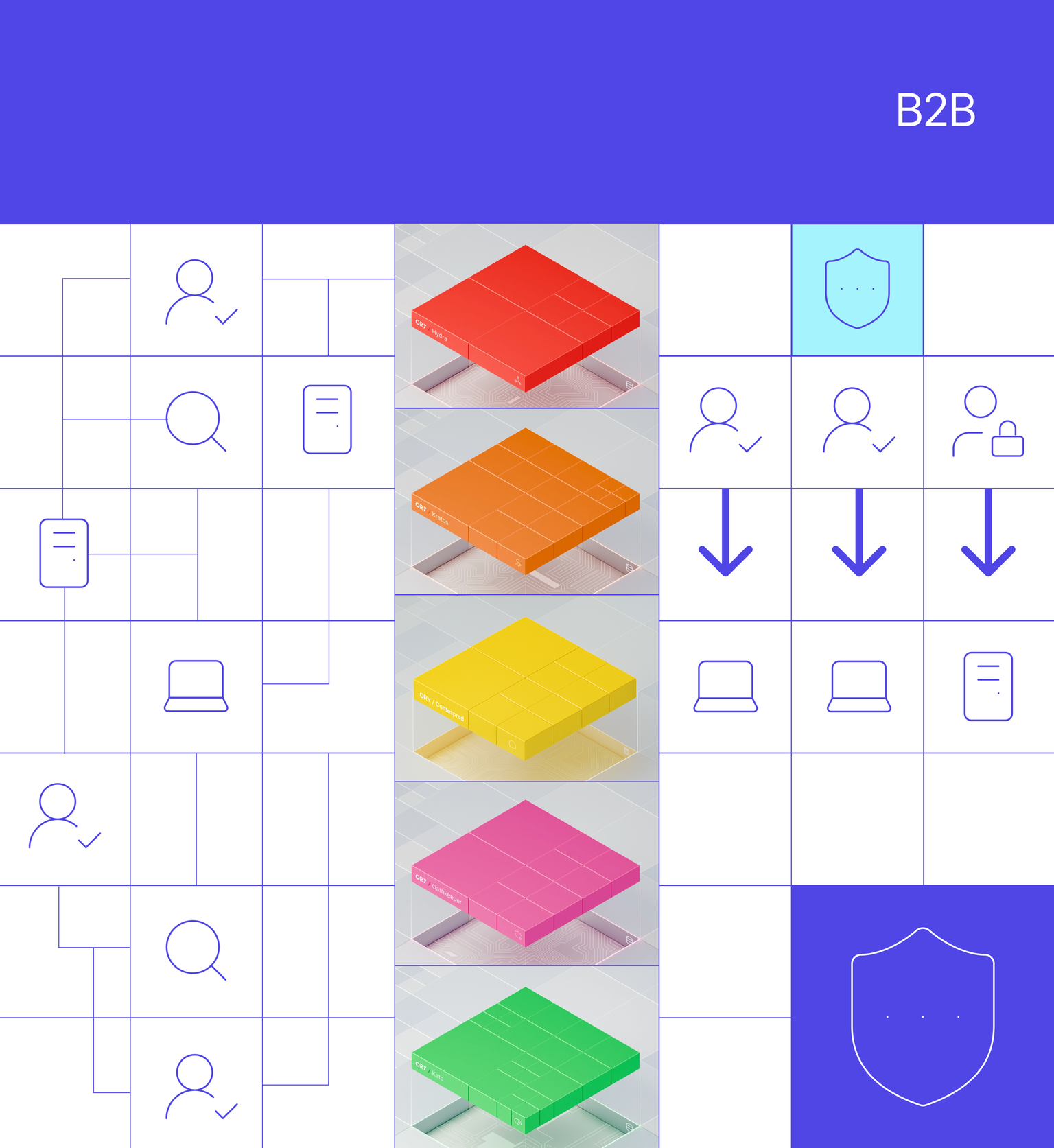
Challenges of B2B Identity and Access Management
Secure access without frustrating partners
A poor B2B access experience erodes trust, diminishes productivity, and increases security risks. Secure and friction-free access is ideal.
Complexity of diverse partner groups
Managing diverse B2B relationships is a complex, continuous cycle of onboarding, updating access, and securely offboarding partners.
Privlege sprawl
Over-permissioning is a common and significant problem that increases security risks, creates compliance violations, and hinders operational efficiency.
Data privacy and compliance
Balancing data privacy regulations and high performance is an often underestimated challenge when building multi-region infrastructure.
Integrations and legacy systems
Modern B2B IAM implementations are challenged by a wide variety of new and old external systems and identity providers (IdPs) that add expense and time to any project.
Why Ory for B2B IAM?
Ory offers a modern approach - secure and seamless UX, granular permissions, and an API-first approach. Own your B2B IAM.
Self-serve onboarding
Enable business partners to self-onboard via easy to follow configuration clicks. Save time, save people, and decrease time to value.
Remove log-in friction and improve security
Social logins, passkeys, SSO, passwordless, WebAuthn, adaptive auth enable you to secure partner access without adding interruptions.
Mitigate risk with granular permissions
Ory provides precise, least-privilege access with flexible policies, centralizing authorization into one platform that allows you to add rules without changing application code.
Take a headless, API-first approach
By decoupling the UI from the backend, we provide unmatched flexibility, performance, and security, allowing developers to create across any platform.
Global compliance without the hassle
Global database replication keeps partner data consistent and unified across all regions, eliminating synchronization issues and providing a single point of administration.
Deployment flexibility - your choice
From Self-hosted to SaaS, Ory provides the same functionality. Start one way and evolve to another, with Ory you have choice and versatility in how you implement.
Our goal was to provide a unified, secure, and consistent user experience across all buying, selling, and brokering groups with the ability to learn, adapt, and customize to user preferences and tendencies.


Tamer Shlash
Software Engineer
Deploy it your way
Self-hosted to SaaS: full control over your infrastructure, data, and compliance.
Dive deeper into specific topics
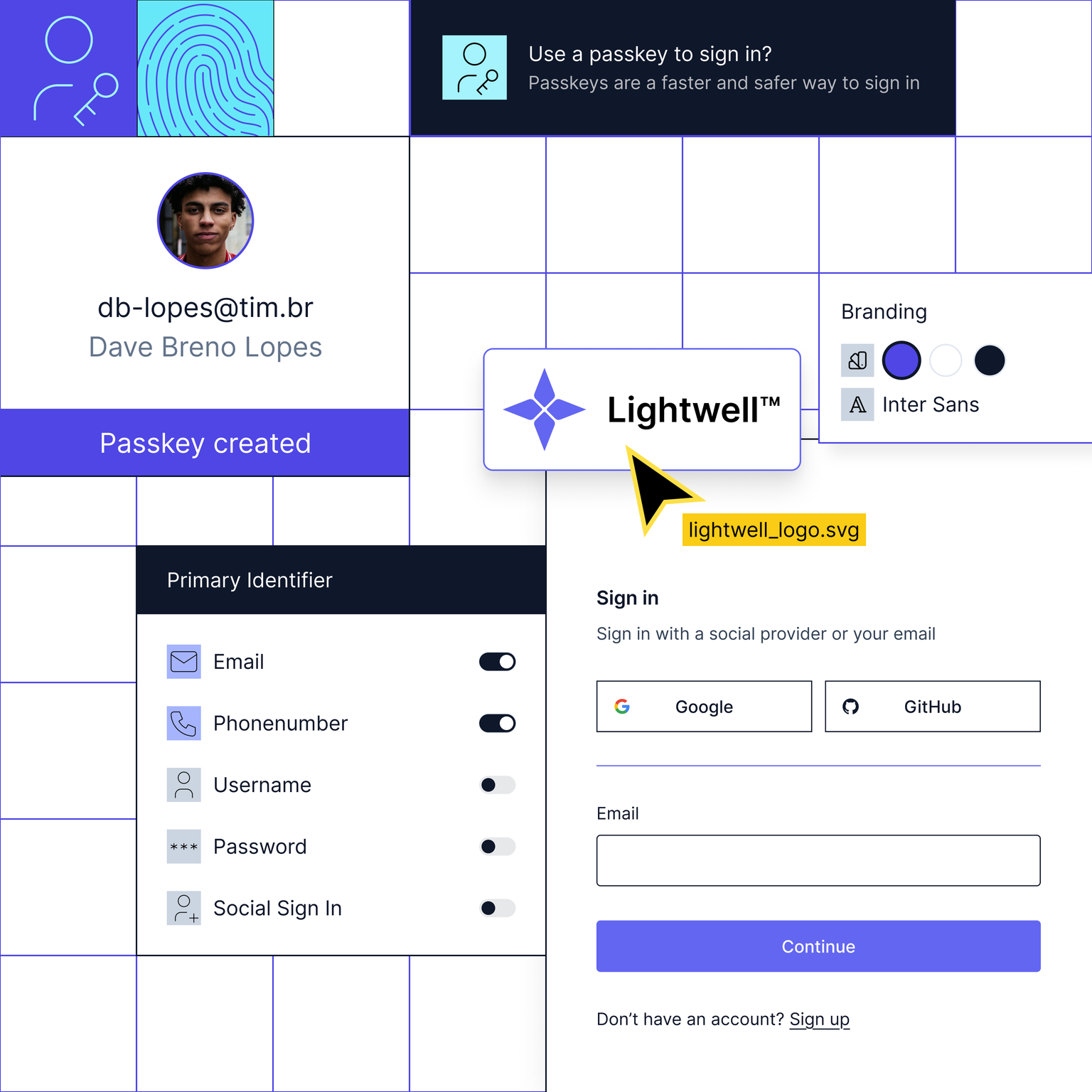
Modular and modern IAM & CIAM
Open-source powered, fully customizable Identity and Access Management solutions. Use them all or bolt-on individual solutions to satisfy your critical use cases