Enterprise SSO and identity federation is challenging. With Ory Polis, you avoid headaches and connect identity providers and directories within days rather than months.
Enterprise readiness for B2B SaaS apps
Ory Polis eliminates the need for technical expertise by providing a developer-friendly solution that lets companies meet enterprise requirements without diverting resources from core product development.

Ahmed Elkaffas
Founder
Seamless Enterprise SSO integration with the customer's existing infrastructure, and minimal effort from the customer side, was very important for us.
Ory Polis features at a glance
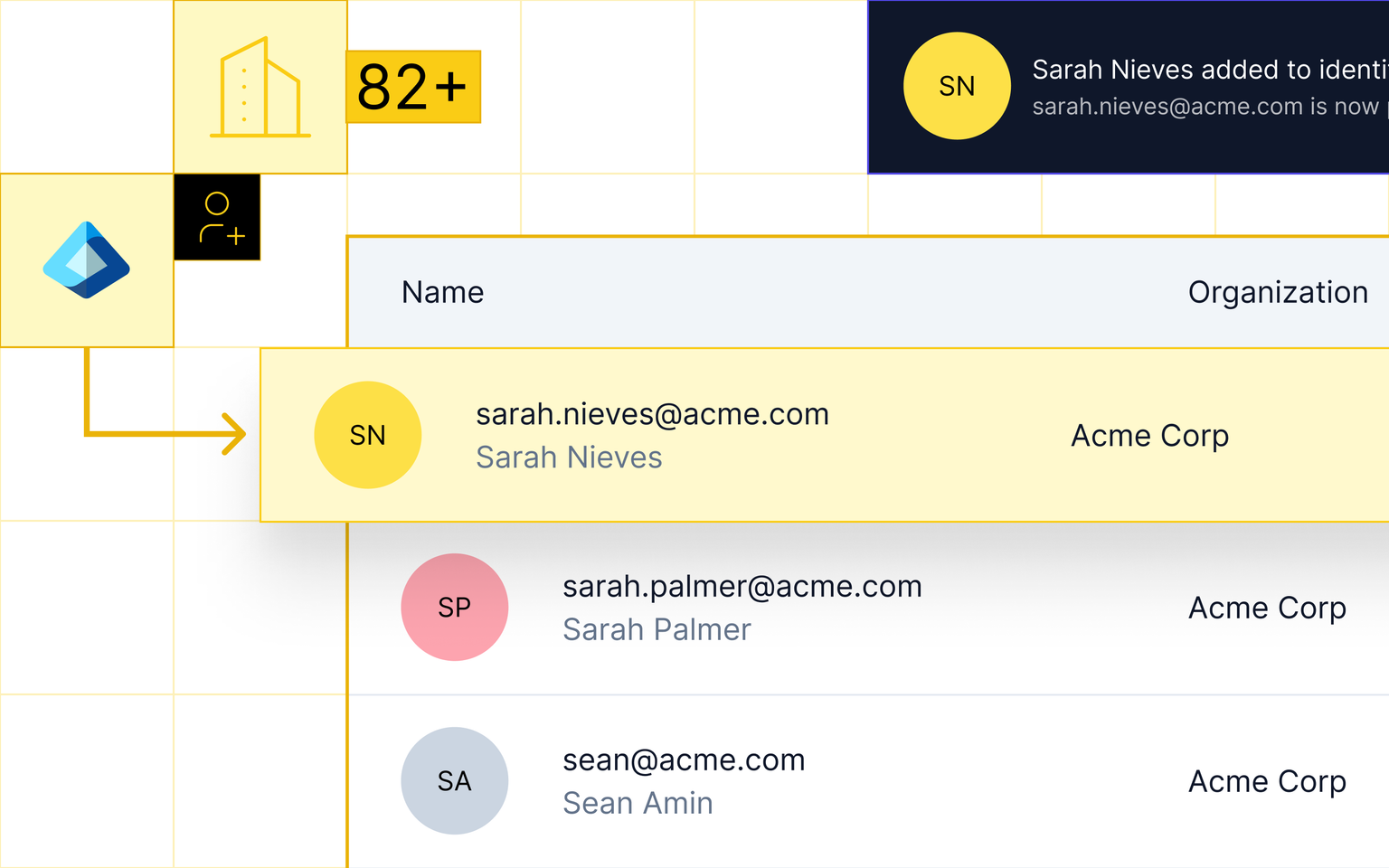
Organizations
Group users within your project, manage SSO connections, and enforce domain-based authentication that integrates with existing identity providers.
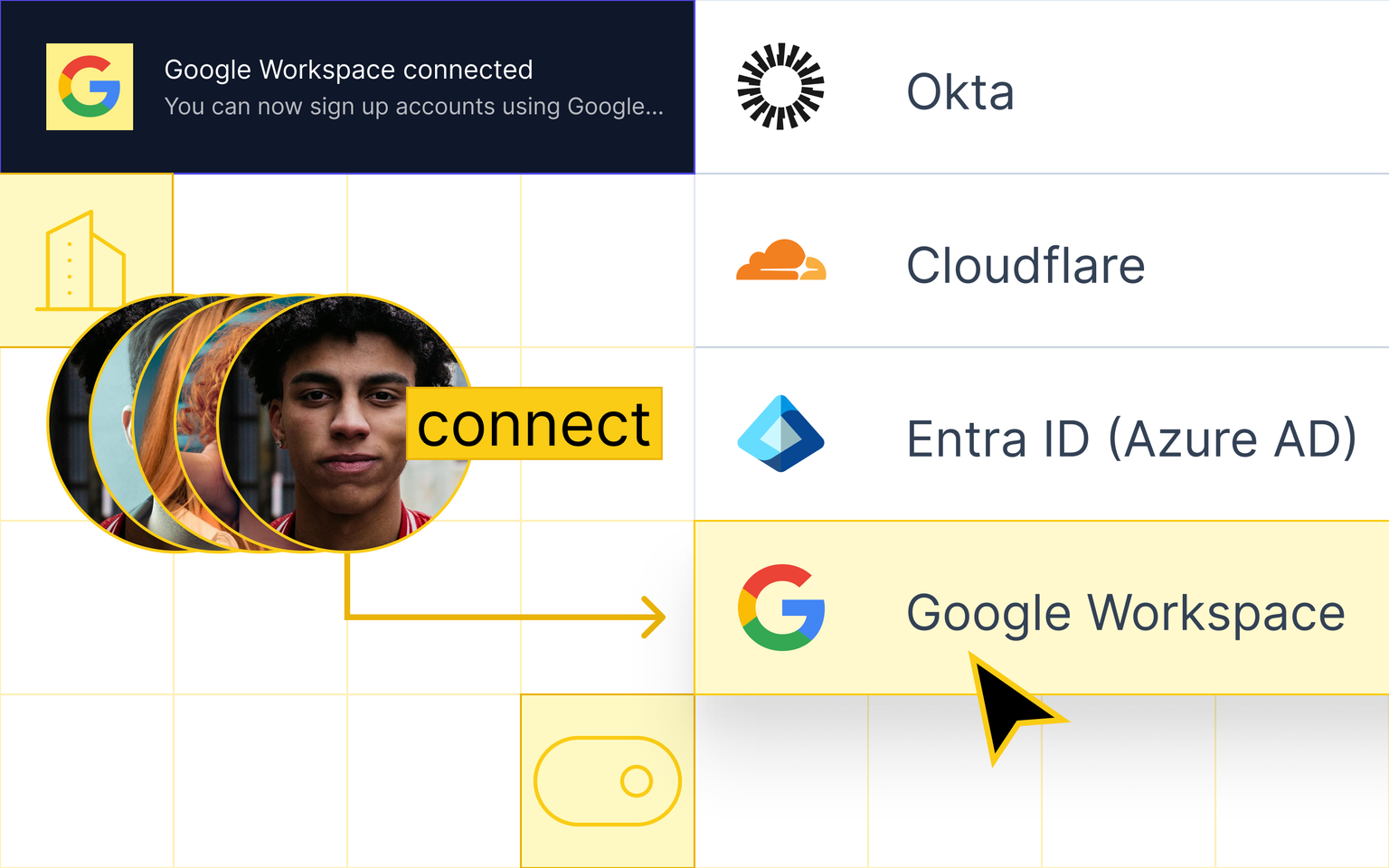
OIDC single sign-on
Establish multiple OpenID Connect (OIDC-based) single sign-on connections for each organization, configurable through the Ory Console and API interfaces.
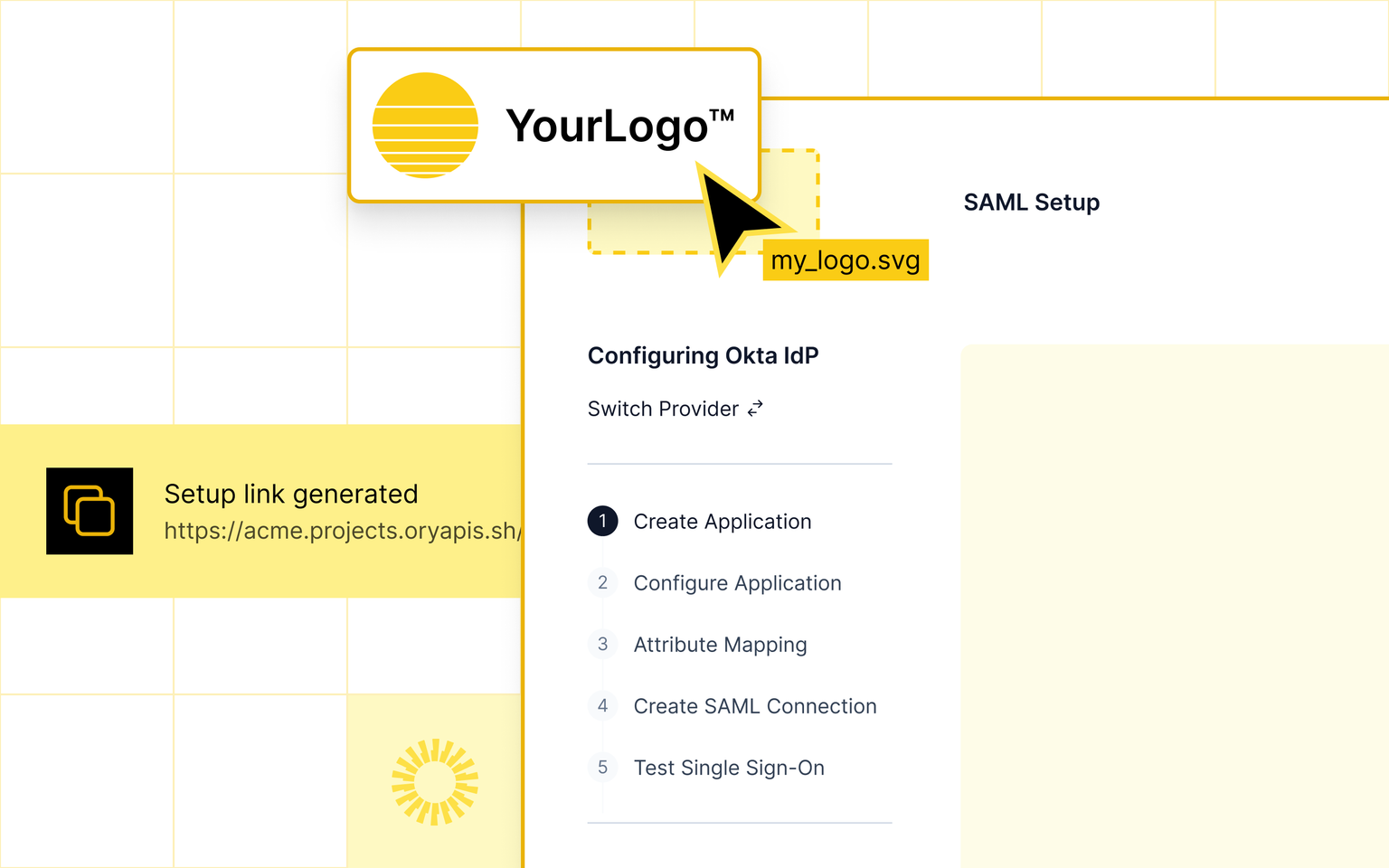
SAML support
Connect with SAML-based identity providers such as Microsoft Entra ID, Microsoft ADFS, Okta, Auth0, Google Workspace, Ping Identity, and more.
SAML to OIDC bridge
Our bridge enables cross-protocol Identity Federation, enabling your app to use modern OIDC internally while still accepting SAML connections from enterprise customers.
Identity Provider discovery
Route users to their SSO provider based on email domain, eliminating manual selection steps for seamless authentication across B2B and B2B2C apps.
Flexible deployment
Deploy anywhere to meet regional data sovereignty and compliance requirements. Ory offers complete deployment flexibility whether self-hosted, private cloud, or on-premises
How to de-risk identity at scale with Ory
OSS is where most teams start. The question is whether it holds up as scale, compliance, and security requirements grow. Running identity infrastructure yourself means owning everything, from patches to incident response, compliance controls, and performance tuning. At enterprise scale, that overhead competes with product innovation. Ory's commercial offerings, OEL and Ory Network, trade that burden for SLA-backed support, managed CVE patching, and audit-ready controls.
OSS
OEL
Ory Network
Ory Polis FAQ
Deploy Ory Polis on your preferred infrastructure
Deploy on any infrastructure and take full control over your organizational and enterprise customer SSO.
Ready to try Ory Polis?
Get started with the guides and docs below
...
const signIn = async () => {
// store the from url before redirecting ... we need this to correctly initialize the oauthClient after getting redirected back from SSO Provider.
localStorage.setItem(APP_FROM_URL, from);
// Initiate the login flow
await authClient?.fetchAuthorizationCode({
tenant,
product,
});
};
const signOut = async (callback: VoidFunction) => {
authClient?.reset();
setUser(null);
callback();
};